Ctrl-Q is open source and you have access to all source code.
It is your responsibility to determine if Ctrl-Q is suitable for your use case.
The creators of Ctrl-Q, including Ptarmigan Labs, Göran Sander or any other contributor, can and must never be held liable to past or future security issues of Ctrl-Q.
If you have security concerns or ideas around Ctrl-Q, please get involved in the project and contribute to making it better!
If you discover a serious bug with Ctrl-Q that may pose a security problem, please disclose it
confidentially to security@ptarmiganlabs.com first, so it can be assessed and hopefully fixed
prior to being exploited.
Please do not raise GitHub issues for serious security-related doubts or problems.
Virus scanning
Every time a Ctrl-Q release is done the created binaries are sent to VirusTotal for scanning.
VirusTotal acts as an aggregated virus scanner that sends the Ctrl-Q binaries to dozens of anti-virus scanners, including many of the major/most widely used ones.
Links to the VirusTotal scan report are included in each release notes, making it easy to check the status of each binary:

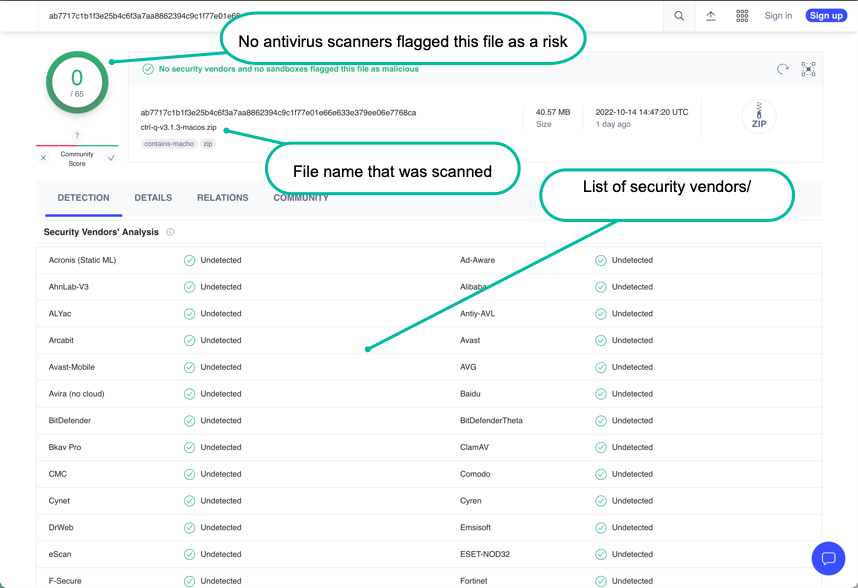
A VirusTotal scan that reports “no risks found” can look like this:
Positive scan vs false positives
If one or more of the security vendors used by VirusTotal reports an issue you have to make a decision.
Is it a real issue or a false positive?
You have to decide this yourself, but some general lines of thought can be:
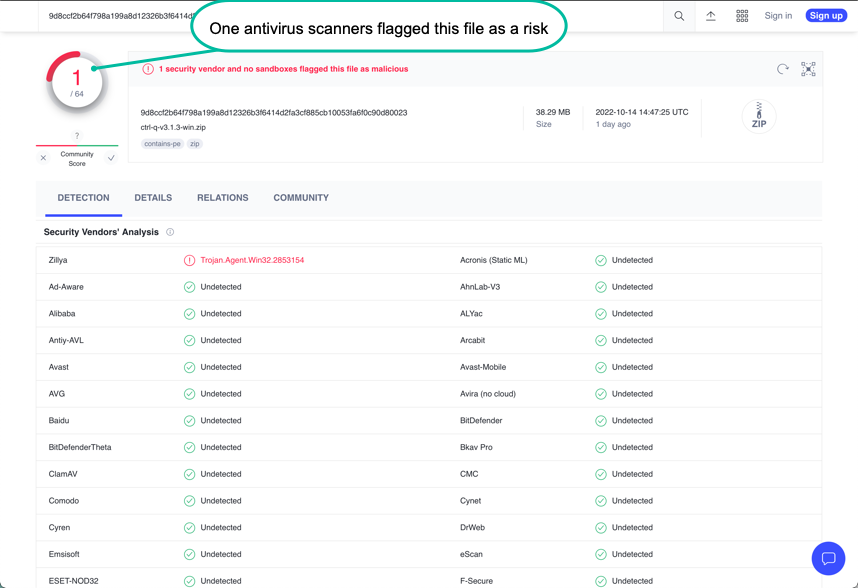
Is it a single vendor that reports the Ctrl-Q binary file to be a risk, or several vendors?
If one vendor reports an issue and 60+ vendors don't, you might be looking at a false positive.
But again - at the end of the day it’s you that must make that decision.
A scan where a single security vendor reports an issue can look like this:
Signed binaries
The macOS executable binary is signed and notarized by Apple’s standard process.
A warning may still be shown first time the app is started. This is expected and normal.
The Windows executable binary is signed by “Ptarmigan Labs AB”.